How to Manage Copyright Assets for Legal Protection
- Feb 26
- 9 min read
Protecting copyright assets in fast-moving technology sectors demands more than basic awareness. For international consultants advising startups and SMEs in innovative fields, especially in Italy and the United Arab Emirates, the challenge lies in mastering both documentation and compliance across diverse legal systems. By developing a thorough catalog and adopting robust digital protection measures, you build a foundation that supports rights enforcement, minimizes legal risks, and positions your clients for sustainable growth in competitive markets. Effective copyright asset management is now a business necessity rather than an afterthought.
Table of Contents
Quick Summary
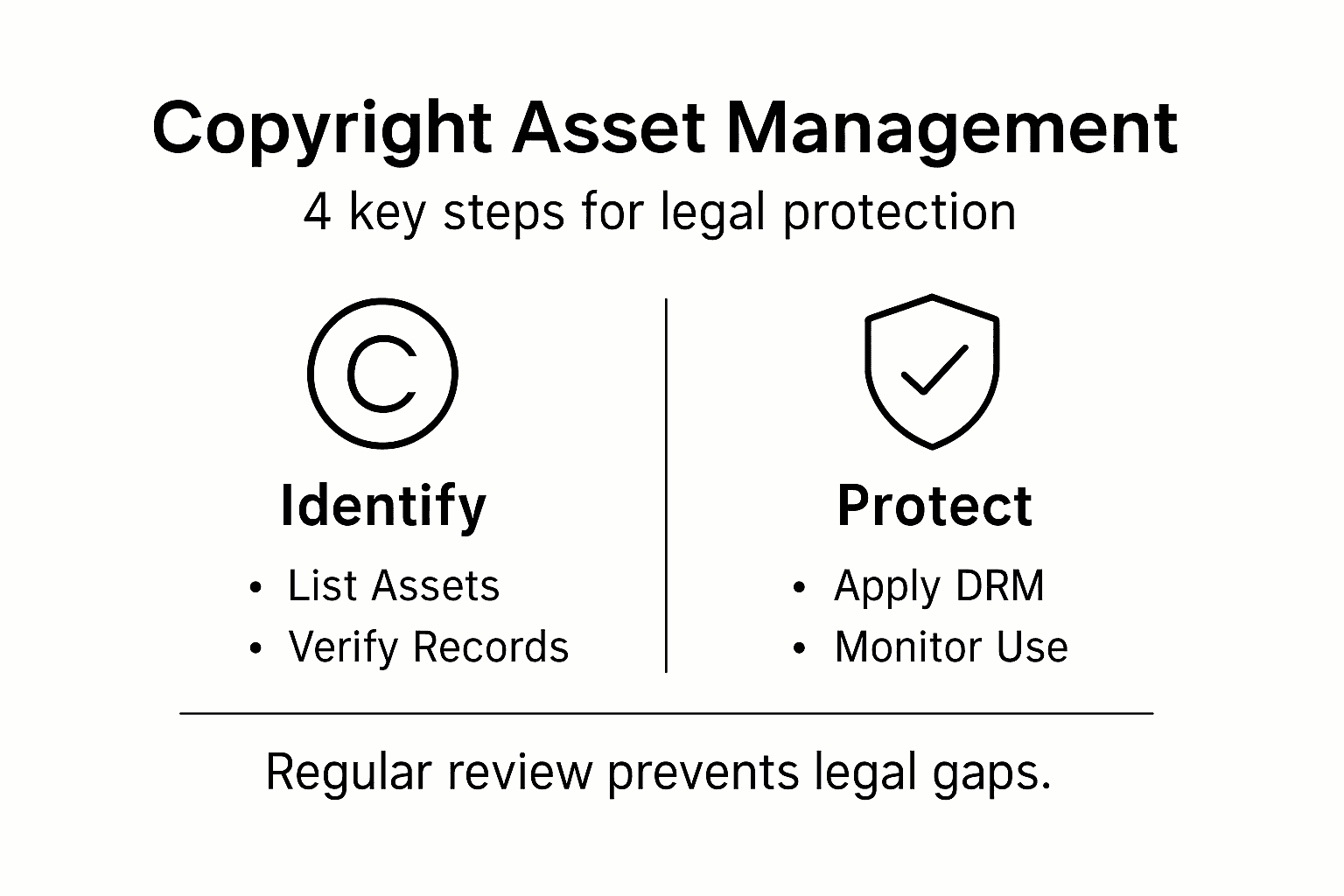
Key Point | Explanation |
1. Catalog Your Copyrighted Assets | Document all creative works to establish ownership and simplify legal protection. |
2. Implement Effective DRM Solutions | Utilize technology to control content access and prevent unauthorized use of your assets. |
3. Actively Monitor Copyright Infringement | Set systems to detect unauthorized use, preserving your legal rights through proactive monitoring. |
4. Regularly Review Your Copyright Strategies | Conduct annual assessments to adapt to changes in copyright law and emerging threats. |
Step 1: Identify and Catalog Copyrighted Assets
Before you can protect your copyright assets legally, you need to know exactly what you own. This step involves conducting a thorough audit of your creative works and documenting each one with precision.
Start by listing all the creative materials your company has produced. For technology-focused startups and SMEs, this typically includes software code, documentation, user interface designs, marketing materials, technical specifications, and any written content created for your platform or applications.
Document the basics for each asset:
Title and description of the work
Date of creation or publication
Author or creator information
Type of work (software, written content, graphics, database, etc.)
Current ownership status
Any registrations already filed
Use copyright office public records to verify existing registrations and check for any competing claims. This searchable database provides registration details dating back to 1898, giving you a complete picture of what’s already protected.
For assets created by your team, establish a centralized system to track registration details. Many international firms managing copyrights across multiple jurisdictions benefit from consistent documentation. Your catalog should capture whether each work is registered, in what countries, and when registrations expire.
When reviewing ownership, confirm that all works were properly created as “works made for hire” under employment agreements. This prevents future disputes over asset ownership, particularly critical when working with contractors or international teams in different legal contexts.
Search copyright records and transfer documentation to understand the complete ownership chain. Identifying gaps in your documentation now prevents expensive legal complications later.
Your copyright catalog becomes your legal foundation. Without it, proving ownership during disputes becomes exponentially more difficult and costly.
Pro tip: Create a spreadsheet with columns for asset name, creation date, creator, registration number, and registration jurisdiction. Include this in your standard IP management process from day one so cataloging becomes automatic as your team creates new assets.
Here is a summary of copyright asset types with common ownership considerations:
Asset Type | Common Ownership Issue | Key Registration Jurisdiction |
Software Code | Contractor vs. employee authorship | United States, EU |
Marketing Materials | Multiple contributors, unclear transfers | United States |
User Interface Design | Collaborative design, work-for-hire status | European Union |
Documentation | Freelancers’ IP rights | United Arab Emirates |
This table compares popular DRM strategies and their business impact:
DRM Strategy | Risk Mitigated | Business Impact |
Encryption | Data theft, unauthorized copying | Increases user trust |
Digital Watermarking | Untraceable leaks | Simplifies legal enforcement |
Licensing Agreements | Misuse, over-distribution | Clarifies user rights |
User Authentication | Shared or stolen access | Reduces support costs |
Step 2: Implement Digital Rights Management Solutions
Digital Rights Management (DRM) protects your copyrighted assets in the online environment where most infringement occurs. This step focuses on deploying technological and legal safeguards to control how your content is used, distributed, and accessed.
Start by understanding what DRM does. Technological protection measures like encryption and licensing agreements govern access to your digital works and prevent unauthorized copying. For technology companies managing software, databases, or digital content, DRM creates a legal framework that makes infringement harder and more traceable.

Identify which of your assets need DRM protection first. Not every copyright requires the same level of security. Software code, proprietary databases, and high-value digital products demand stronger protection than published marketing content.
Implement these core DRM strategies:
Encryption of sensitive files and databases to prevent unauthorized access
Licensing agreements that specify permitted uses and distribution rights
Content management systems that track downloads and restrict sharing
Digital watermarking to identify ownership and detect unauthorized copies
User authentication systems that limit access to authorized parties only
When working internationally, particularly across European Union jurisdictions and United Arab Emirates markets, ensure your DRM complies with local copyright laws. The European Union Digital Copyright Directive and similar regional frameworks shape what DRM implementations are legally enforceable.
Digital content protection and encryption have become essential as piracy and unauthorized sharing challenge copyright enforcement. Balance robust protection with user experience—overly restrictive DRM can frustrate legitimate users and damage your brand.
For startups and SMEs, consider cloud-based DRM solutions that don’t require significant infrastructure investment. These platforms handle encryption, licensing, and access control automatically as your team creates and distributes new works.
Effective DRM transforms your copyrights from passive legal claims into actively enforced protections that deter infringement before it happens.
Pro tip: Combine DRM technology with clear terms of service and licensing agreements that customers can easily understand. Many infringements stem from users who don’t realize restrictions exist, not malicious actors, so transparency strengthens both protection and legal defense.
Step 3: Monitor and Enforce Copyright Protection
Monitoring your copyrighted assets actively prevents infringement from escalating and strengthens your legal position if disputes arise. This step involves setting up systems to detect unauthorized use and understanding your enforcement options.
Begin by establishing a monitoring routine. Track where your copyrighted materials appear online, who is using them, and whether they have permission. For software companies, this means checking app stores, code repositories, and competitive products. For content creators, monitor distribution channels, social media platforms, and resale sites.
Set up Google Alerts for your major works and brand terms. Use reverse image search tools for visual content. Monitor torrenting sites and file-sharing platforms where your digital products frequently appear. Establish a schedule to conduct these checks systematically, not randomly.
Create an enforcement action plan:
Document each infringement with screenshots, URLs, and timestamps
Verify that the use violates your copyright and is not fair use
Compile evidence of ownership from your copyright registration files
Assess the severity and scope of the infringement
Determine whether to send a cease-and-desist letter or pursue litigation
Understand the legal framework available to you. Copyright infringement remedies and enforcement procedures under Title 17 of the United States Code include monetary damages, injunctions, and statutory damages in registered works. The Digital Millennium Copyright Act provides additional tools for combating circumvention of technological protections.
Copyright registration strengthens enforcement significantly. Registered copyrights allow you to pursue statutory damages and attorney fees in court, making infringement costly for violators. Without registration, you can only recover actual damages, which are difficult to quantify.
When you discover infringement, your response matters. Start with a professional cease-and-desist letter. Many infringers stop immediately when they understand the legal risk. If informal resolution fails, work with a legal team experienced in intellectual property enforcement to evaluate litigation or settlement strategies.
For international startups managing copyrights across multiple jurisdictions, understand that enforcement varies significantly. European Union protections differ from United States protections, and enforcement in the United Arab Emirates follows its own legal procedures.
Active monitoring transforms copyright from theoretical rights into concrete protections that deter infringement before significant damage occurs.
Pro tip: Use monitoring software that tracks digital copies automatically rather than relying solely on manual searches. Many platforms offer affordable subscription services designed specifically for creative professionals and tech companies managing distributed content across multiple channels.
Step 4: Review and Update Copyright Strategies
Copyright law and technology evolve constantly. Your protection strategies must evolve with them, or gaps will emerge that threaten your assets. This step involves systematically reviewing your copyright approach and updating it to address new challenges.
Start by conducting an annual review of your copyright portfolio. Examine which works have been registered, which remain unprotected, and whether your DRM systems are still effective. Technology shifts rapidly, especially in software and digital content sectors where your startup or SME operates.
Evaluate emerging threats specific to your industry. Artificial intelligence tools now generate content that mimics styles and formats, creating new infringement risks. Public domain expansion means some older works lose protection while new works continuously enter the system. Understanding these shifts helps you prioritize your protection efforts.
Review these critical areas:
Registration status of all major copyrighted assets
Effectiveness of your current DRM technologies
Changes in relevant copyright laws affecting your jurisdiction
New distribution channels where your content appears
Licensing agreements and whether they reflect current business practices
Enforcement actions taken and their outcomes
Stay informed about regulatory changes. Copyright strategies must adapt to technological innovation and emerging issues like artificial intelligence and shifting licensing models. European Union directives, United States Copyright Office guidance, and United Arab Emirates regulations all change periodically and affect your protection approach.
Consider scheduling quarterly monitoring sessions rather than waiting for annual reviews. This approach catches problems earlier and prevents small gaps from becoming major vulnerabilities. Update your internal documentation as policies change.
Strategic copyright planning involves continuous adaptation to technological changes and evolving legal frameworks. Consult with intellectual property counsel annually to ensure your strategies remain aligned with current law and best practices.
For international operations, maintain separate review schedules for different jurisdictions. Italian copyright law evolves independently from United States law. Your strategy in one market may not fully protect assets in another.
Static copyright strategies become obsolete. Periodic reviews transform protection from a one-time effort into a sustainable, evolving practice.
Pro tip: Create a calendar reminder for quarterly portfolio reviews and annual legal consultations. Assign one team member responsibility for monitoring copyright news and regulatory changes in your primary markets, ensuring your strategy stays current without requiring constant executive attention.
Protect Your Copyright Assets with Expert Legal and Technical Support
Managing and enforcing your copyright assets can feel overwhelming with complex registration requirements, evolving DRM technologies, and the need for constant monitoring to prevent infringement. This article highlights key challenges such as cataloging ownership, implementing Digital Rights Management, and staying updated with changing laws — crucial steps to avoid costly disputes and protect your intellectual property effectively.
Don’t let unclear ownership or weak protection expose your assets to infringement risks. At Studio Legale Coviello, we specialize in tailored legal and technological consulting for startups and international SMEs. Our expertise in intellectual property law, combined with innovative tools like artificial intelligence and a dedicated IP management app, ensures your copyrights, trademarks, and patents receive comprehensive, cutting-edge protection.
Take control of your copyright strategy today. Visit Studio Legale Coviello to explore how our advanced solutions can safeguard your valuable assets, streamline registration processes, and enforce your rights worldwide. Empower your business with trusted legal counsel and modern technology—act now to secure your creative future.
Frequently Asked Questions
How can I identify and catalog my copyrighted assets?
To identify and catalog your copyrighted assets, start by listing all creative materials your company has produced, such as software code, marketing materials, and written content. Create a detailed record for each asset, including the title, date of creation, author information, and ownership status. Aim to complete this cataloging within 30 days to ensure accurate tracking.
What are effective Digital Rights Management (DRM) strategies for protecting copyright assets?
Effective DRM strategies include implementing encryption for sensitive files, establishing licensing agreements that outline usage rights, and using digital watermarking to deter unauthorized use. Evaluate which assets need stronger protection first, and aim to set up these systems within 60 days to minimize risk.
How should I monitor for copyright infringement?
To monitor for copyright infringement, establish a regular routine to track where your assets appear online and identify any unauthorized use. Utilize tools like Google Alerts and image search programs, and schedule these checks weekly to catch potential violations early.
What should I include in my copyright enforcement action plan?
Your copyright enforcement action plan should include documenting each infringement with evidence like screenshots and URLs, verifying that the use violates your copyright, and outlining whether to issue a cease-and-desist letter. Develop this plan immediately after monitoring for infringements to stay proactive and organized in your response.
When should I review and update my copyright strategies?
You should review and update your copyright strategies annually or more frequently in response to significant changes in technology or legal standards. Schedule quarterly reviews to ensure that your copyright portfolio remains current, and adjust your protections based on new threats or changes in copyright laws.
How can I ensure proper ownership of my copyrighted works?
To ensure proper ownership of your copyrighted works, confirm that all creations are classified as “works made for hire” under employment agreements, especially for work done by contractors. Review your documentation regularly to prevent ownership disputes and clarify who holds the rights to each asset.
Recommended






Comments